By Ronen Bergman and Declan Walsh – The New York Times –
A series of sophisticated cyberattacks targeting Egyptian journalists, academics, lawyers, opposition politicians and human rights activists has been traced to Egyptian government offices, a cybersecurity firm has found.
The attackers installed software on the targets’ phones that enabled them to read the victims’ files and emails, track their locations, identify who they contacted and when, according to a report published Thursday by Check Point Software Technologies, one of the biggest cybersecurity companies in the world, with headquarters just south of San Francisco and in Tel Aviv.
Two activists who were targeted by the cyberattack were arrested in a roundup of prominent opposition figures last month as part of Egypt’s crackdown on antigovernment protests.
Check Point found that the central server used in the attacks was registered in the name of the Egyptian Ministry of Communications and Information Technology and that geographic coordinates embedded in one of the applications used to track the activists corresponded to the headquarters of Egypt’s main spy agency, the General Intelligence Service.
The cyberattack began in 2016, according to the Check Point report. The number of victims is unknown but Check Point identified 33 people, mostly well-known civil society and opposition figures, who had been targeted in one part of the operation.
“We discovered a list of victims that included handpicked political and social activists, high-profile journalists and members of nonprofit organizations in Egypt,” said Aseel Kayal, a Check Point analyst.
The Egyptian government did not respond to a request for comment for this article.
The attack was the second Egyptian internet subterfuge operation to recently come to light.
A covert Egyptian campaign to build support for Sudan’s military using fake social media accounts was exposed in August. The operation was run by a company with links to the Egyptian government.
The cyberattack on the phones and email accounts of activists employed a shifting array of slick software applications to trick users.
An app for Gmail, called Secure Mail, informed targets that their accounts had been compromised, then lured them into revealing their passwords.
Another, called iLoud200%, promised to double the volume of cellphones. Instead, it gave the attackers access to the telephone’s location, even if the user turned off location services.
One of the more sophisticated apps, IndexY, claimed to be a free app for identifying incoming callers, along the lines of the well-known app Truecaller. But the app also copied the details of all calls made on the phone to a server controlled by the attackers, Check Point found, with the emphasis on the users’ communications with parties outside of Egypt.
Since its release early this year, IndexY became a popular app in the official Google Play Store, where it was downloaded 5,000 times.
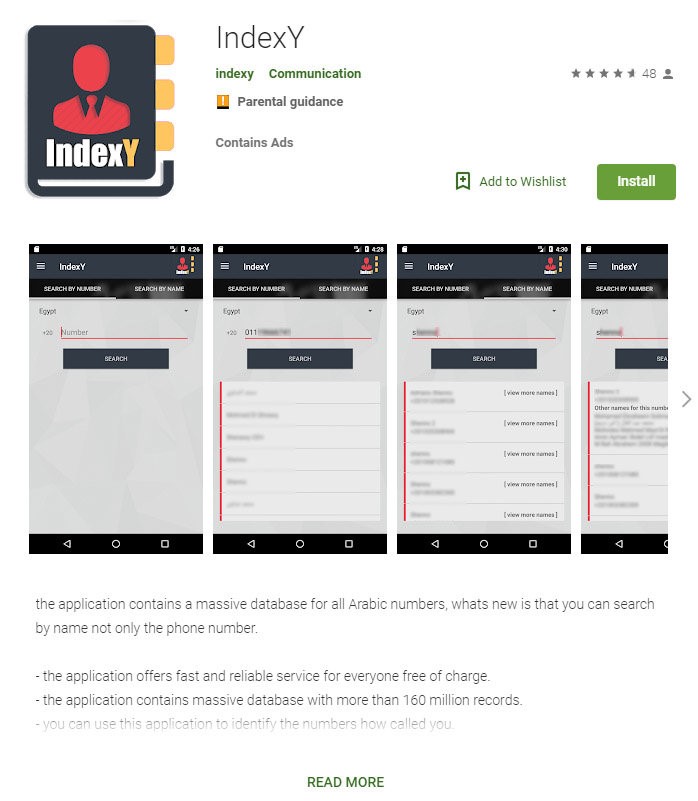
IndexY claimed to be a free app for identifying incoming callers. But it also copied the details of all calls made on the phone to a server controlled by the attackers, Check Point found. Credit via Check Point
Just getting placed in the Google Play Store, circumventing the measures Google takes to vet new apps, testifies to its high degree of sophistication and the extensive efforts invested in its development, the Check Point researchers said. The application was available on the Google Play store until Check Point on July 15 raised its concerns with Google, which removed the app and “banned the associated developer” about two weeks later.
Despite their skill and resourcefulness, the perpetrators appear to have made a number of mistakes that allowed Check Point to track the apps’ origins.
The pages and sites used to carry out the attacks were all connected to an IP address belonging to a Russian telecommunications company called Marosnet, and to a central server registered to “MCIT,” an apparent reference to Egypt’s Ministry of Communications and Information Technology.
The iLoud200% app, like most geolocation software, had default coordinates, a point that is generally set at the time and place of its initial activation by the developers. The default coordinates in the app matched those of the headquarters of the General Intelligence Service, Egypt’s equivalent of the C.I.A.
Check Point officials said it was possible that the coordinates had been planted in the app as a false flag by someone trying to implicate the Egyptian state. But a more likely explanation, they said, was that the coordinates had been accidentally left in the server out of sloppiness by the people running the operation.
A Check Point official said that other clues also pointed to state involvement in the attacks. The campaign’s multiyear duration, as well as the vast amounts of data collected, required significant financial and human resources. And the targets of the attack, who appear to have been selected for their political activity or beliefs, do not align with traditional cybercrime motivations, which tend to focus on extracting money.
In addition, Ms. Kayal said, the investigation suggested that the perpetrators were Arabic speakers and the default time used in the apps was Egyptian time.

One victim of the cyberattack, Dr. Shady al-Ghazaly Harba, a surgeon and opposition activist, is in prison on charges of insulting the president and spreading false news. Credit Tara Todras-Whitehill for The New York Times
Two of the victims identified by Check Point were arrested after scattered protests erupted against Egypt’s president, Abdel Fattah el-Sisi, last month: Hassan Nafaa, a political scientist at Cairo University, and Khaled Dawoud, a former journalist and leader of the secular Constitution Party, a prominent el-Sisi critic.
A third victim, Dr. Shady Al-Ghazaly Harb, a surgeon and opposition activist, was detained in May 2018 for his criticism of the government on Twitter. He is currently in solitary confinement at a prison in Cairo where he faces charges of insulting the president and spreading false news.
The Check Point investigation began after Amnesty International reported in March that a number of Egyptian civil rights activists were the target of a state-sponsored phishing campaign in an effort to obtain the victims’ email passwords. Amnesty concluded that the attacks were “most likely” carried out by, or on behalf of, the Egyptian authorities.
The Check Point investigation found that the attacks were broader than those initially reported by Amnesty and provided detailed evidence suggesting that the Egyptian government was the likely perpetrator.
“These targeted surveillance campaigns represent an escalation of the tactics employed by Egyptian authorities in their systematic efforts to intimidate and silence civil society in the country,” Danna Ingleton, deputy director of Amnesty’s internet rights program, said Wednesday. “Instead of developing new means to crush dissent, the authorities must end their relentless onslaught against human rights defenders and respect the rights to freedom of expression and association.”
The target list of 33 people that Check Point retrieved from the attack server includes Egyptians living in Canada, Britain and the United States. Several said they already knew their email had been targeted because of warnings from Google or rights groups like Amnesty International and Human Rights Watch.
Medhat al-Zahed, a leader of the Socialist Popular Alliance party, said he had stopped using the email listed on the attack server after realizing it had been compromised. “I am worried, of course, because it violated my privacy,” he said. “But not more than that, because everything in my life is open.”
For some activists, attempts to hack their email or cellphones represent just one more aggravation of life in Egypt under Mr. el-Sisi, where critics and activists risk arrests, long spells in prison, travel bans and having their assets frozen. Many have been smeared in stories in pro-state news media.
Ragia Omran, a prominent lawyer and human rights activist, said she had been repeatedly warned by researchers with human rights groups that her communications had been targeted. “I am always worried,” she said in a text message. “I don’t communicate anything too confidential on email.”
An official with the Egyptian-Canadian Coalition for Democracy had been targeted after his organization published a video showing an Egyptian government minister making a threatening gesture during a visit to Canada in July.
During a speech in Toronto, the minister for immigration and expatriate affairs, Nabila Makram, said that any Egyptian who publicly criticized the country “will be cut,” while making a slitting gesture across her throat.
Ms. Makram said her remarks had been taken out of context.
Two months later, Google warned the official with the Egyptian-Canadian group that his email account was under attack, the official said, speaking on condition of anonymity to minimize the risk of further attacks.
Afaf Mahfouz, a psychoanalyst and veteran civil society activist living in Florida, also named on the list, said she had been alerted to the attack by Human Rights Watch, probably for her work with women’s groups in Egypt.
“I thought that because of my age they would leave me alone,” said Ms. Mahfouz, who is 81 and suffering from a serious illness. “But I’m not surprised.”
________________________________________